Trezor Login: The Ultimate Guide to Secure Crypto Access
Discover how Trezor Login works, why it’s different from standard password-based logins, and how to securely access your crypto using your Trezor hardware wallet — with full control over your private keys.
💡 What “Trezor Login” Really Means
The term Trezor Login often confuses newcomers. Unlike centralized exchanges or online wallets, Trezor doesn’t store your credentials. Instead, your hardware wallet becomes the “key” that unlocks your crypto — a physical gateway to digital ownership. There’s no username or password, only cryptographic proof that you own the private keys.
🔐 How the Trezor Login Process Works
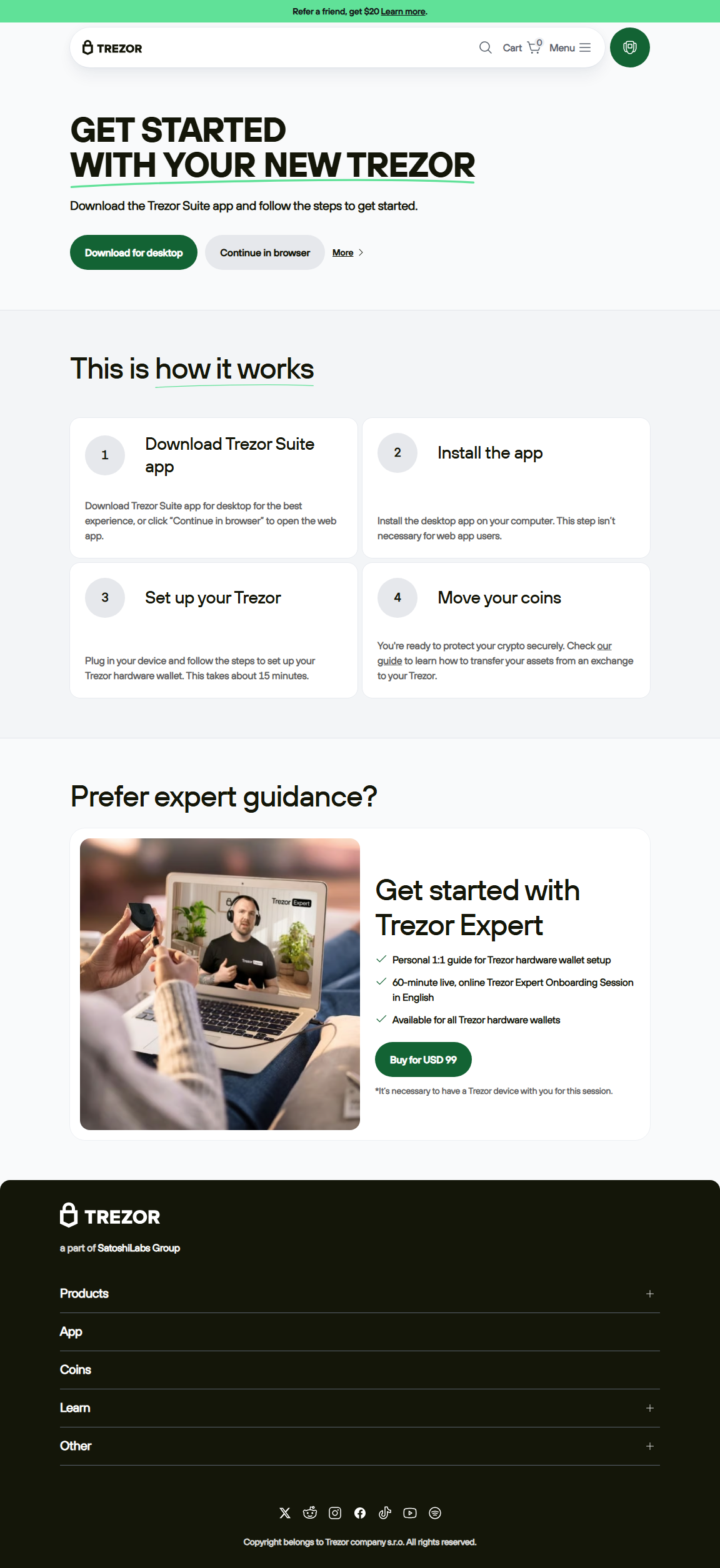
Accessing your wallet involves connecting your Trezor device to Trezor Suite, a desktop or web-based application. The login process is decentralized, meaning your sensitive data never leaves your device.
- Connect your Trezor device to your computer via USB or WebUSB.
- Unlock it using your secure PIN entered directly on the hardware wallet.
- Optionally, add a passphrase for extra wallet layers.
- Confirm actions on your device screen before any transaction executes.
This local authentication ensures your crypto remains safe even if your computer is compromised. Your private keys never touch the internet.
⚙️ Step-by-Step: How to Access Your Trezor Wallet
Step 1: Open Trezor Suite
Go to the official trezor.io/start link or launch your desktop Trezor Suite. Avoid third-party links — phishing attacks mimic Trezor interfaces.
Step 2: Connect Your Device
Plug your Trezor in. Trezor Suite automatically detects it and initiates a secure communication channel.
Step 3: Enter Your PIN
Enter your PIN using the randomized keypad shown on your computer and device screen. It prevents keyloggers from intercepting input.
Step 4: Optional Passphrase
Add a custom passphrase to generate hidden wallets. It’s like a secret layer of encryption over your seed phrase.
🔄 Trezor Login Options Compared
🚫 Avoid These Login Mistakes
- Never enter your recovery seed online — it’s meant for offline device recovery only.
- Check that the site address begins with https://trezor.io before proceeding.
- Do not install unofficial browser extensions or “Trezor login” clones.
- Avoid reusing weak PINs; make them unpredictable.
- Keep firmware updated to patch vulnerabilities and improve compatibility.
🧠 Best Practices for a Safe Trezor Login
- Physically verify wallet addresses on your Trezor screen before confirming any transaction.
- Keep your recovery seed offline and protected from moisture and light.
- Use a passphrase for additional layers of security.
- Download Trezor Suite only from the official Trezor website.
- Disconnect your Trezor when not in use to minimize exposure.
❓ Frequently Asked Questions
1. Do I need an account to log into Trezor?
No. Trezor is a hardware wallet, not an online account. Your access depends entirely on your device, PIN, and recovery seed.
2. Can I use my Trezor device on multiple computers?
Yes, safely. As long as you use trusted computers, your private keys remain within the device itself, never the computer.
3. What if I lose my Trezor device?
You can recover your wallet using your 12–24 word recovery seed. This seed is the only way to restore access to your funds.
4. How do I update my Trezor firmware?
Connect your Trezor to Trezor Suite and follow the firmware update prompts. Always verify update sources before proceeding.
5. Is it safe to connect Trezor to MetaMask?
Yes, provided you confirm every transaction on your device. This ensures even if MetaMask is compromised, your assets stay secure.
“Your login is your hardware — your password is your possession.”
With Trezor Login, you’re not just signing in — you’re proving ownership without ever sharing your private keys.
🏁 Conclusion: Redefining Login in the Crypto World
The Trezor Login process isn’t about entering a password; it’s about establishing cryptographic trust between you and your device. This model eliminates centralized vulnerabilities and gives you direct control of your assets. Whether you’re trading, storing Bitcoin, or exploring DeFi, your hardware wallet stands as your fortress of digital security.
Empower your crypto journey by logging in securely — the Trezor way.